The life of an independent consultant as it relates to technology configuration can be murky at times.
In a large organization, it’s usually quite rigid, IT provisions you a machine (that you may, or many not, have a choices in selecting), that they have configured, they’ve established policies and procedures that help guide you to what you can and cannot do (perhaps, “should, or should not, do?”) You have standard software and you are told where and how to store information and collaborate with co-worker, partners and customers. Your tech is monitored for activity (nefarious, or otherwise) and protected from theft with MDM solutions (No, not Master Data Management, but Mobile Device Management) to safe guard corporate IP and assets.
So what about when its just you? … What mood are you in today? … Do you feel like being consistent with where you store stuff? … How long has it been since you’ve backed up that PC? When does my warranty expire for that business critical laptop? Do I have drop protection? Who do I call if I need on-site, next business day repairs? … Oh, I didn’t buy on-site this time?
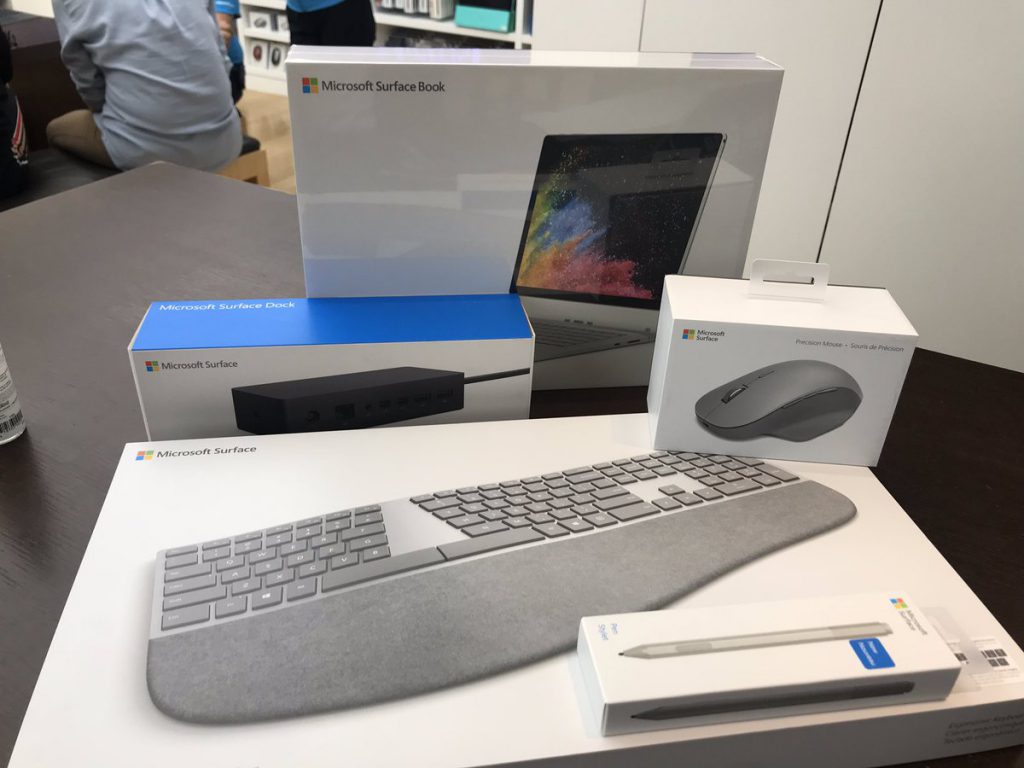
So, as I have recently lost a machine, and fumbled to get my assets together, I have a great opportunity to be more consistent, establish and follow some of those best practices (that I KNOW will inevitably save me time in the future) and document some of my decision/commitments here… for all of you to chime in on, criticize, mock… no, but seriously, your input and suggestions will be appreciated.
So, here is one of those thing that has plagued me for some time. Attaching a machine to an active directory domain. There are new opportunities, especially as many of my clients have an Azure presence. Some are “Federated,” others are synchronized, some are just on-prem and a few are just in the cloud. How do I manage this with my singular machine? Do I really want to connect my machine to an on-premises domain? They will have control of my PC! Who would actually trust my machine anyways? How about Azure AD – does connecting to their Azure AD in this way conception let them “own” my PC? I don’t believe so… Can I have my machine connect to more that 1 Azure AD tenant without causing problems?
Last year I created a VM with VMware Workstation Pro on my PC for a customer I was working with. This worked okay, but at the end of the day, they ended up hosting a “developer workstation” in their VMware infrastructure for me to jump onto to get work done, connecting via VPN first of course.
Should I then have local User Accounts, dedicate to each of my customers, on my machine? Or should simply keep ALL of my customers in one profile?
One thing I AM going to do, as voldemarz recommends doing in this Stack Exchange response:
https://superuser.com/questions/890812/how-to-rename-the-user-folder-in-windows-10
and that is to create a local account FIRST with a name that I’d like reflected in my User home directory… For Example:
C:\Users\ScottStaufferAtOutlook
C:\Users\ScottAtSQLSocialite
C:\Users\ScottAtCustomerABCCorp
C:\Users\ScottAtXyzLtd
These will work fine… the 1st path above being my personal, local admin account for the machine. The 2nd being my community Office 365 Tenant for doing Data Platform work for presentations and demos. The remaining paths are for clients for whom I may or may not be able to connect to the Azure AD tenants (but certainly NOT for traditional, on-prem Active Directory) – If I am required to have a local machine to connect to their on-prem AD, I can set up a VM on my machine or on their VM infrastructure.
Truly, I’d LOVE to hear how YOU have dealt with any of the topics that I’ve raised. In particularly, if you have insight on pro/cons around multiple account on a single machine connecting to different Azure AD tenants – that would be TRULY helpful.
Somewhat related, I did read this for a second time last night… Bob does a great job, both ranting, and explaining the intricacies of Microsoft Person and Work & School Accounts.
http://www.brucebnews.com/2016/06/finding-your-way-through-microsofts-maze-of-work-and-personal-accounts/
[disclaimer – I rely too much on spell check and grammar checking build into WordPress. If something I typed makes you twitch uncontrollably, please let me know so that I can stop your pain 😉 ]
